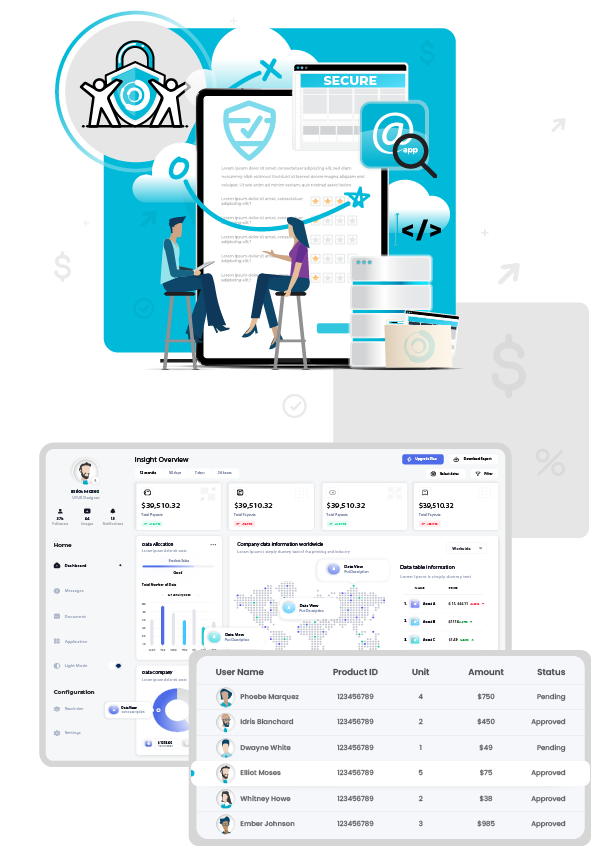
Enterprise Security Built into Every Workflow
Secure data, incentives, payments, and operations with robust, platform-level controls thoughtfully designed for scale, compliance, and long-term trust.

Security that Scales with Your Organization
Protect data, financial workflows, and platform access with enterprise-grade controls designed for global programs.
Data Security Protection
Safeguard sensitive data across interconnected systems and stakeholders.
Secure Transactions
Protect financial workflows, incentives, and payout processing.
Unique Access Control
Enable role-based permissions across distributed program environments.
Global Compliance
Maintain regulatory alignment across industries, regions, and markets.
TRUST CENTER OVERVIEW
At 360insights, Trust is Foundational
Our Trust Center is designed to eliminate the complexity of security evaluations by providing immediate, self-service access to our certifications, compliance documentation, and privacy practices.
By centralizing our enterprise-grade security posture, we reduce friction for your technical teams and deliver real-time assurance to accelerate decision-making and scale your programs with confidence.
Learn how enterprise-grade controls, encryption, and continuous monitoring safeguard data and workflows.
Access details on our adherence to leading standards such as SOC 1, SOC 2, ISO 27001, and more.
See how we embed privacy principles into our platform, ensuring responsible data handling and regulatory alignment.
Understand our collaborative approach, where 360insights secures the platform, and you retain control over program configuration and data usage.
Find FAQs, documentation, and direct access to our compliance and security teams for any additional questions.

Security that Stacks. Protection that Performs.
We implement multiple, risk-based controls to help ensure data confidentiality, integrity, and availability across the platform.
Access & Identity Management
Role-based access controls align system permissions with defined user responsibilities. Secure authentication, authorization protocols, and least-privilege enforcement limit exposure and ensure correct access across platform.
Data Protection
Sensitive program, participant, and financial data is protected through encryption. Combined with strict controls governing how regulated and confidential information is accessed, processed, and stored.
Infrastructure & Application Security
Monitoring & Incident Response
Continuous system monitoring detects unusual activity across the platform. Structured incident response procedures enable rapid investigation, escalation, and remediation aligned with industry security practices.
Security at a Glance
Building Confidence Through Intelligent Control
We help organizations meet compliance standards, protect financial operations, and maintain transparency through strong controls and shared accountability-enabling trusted, scalable growth.

Compliance & Governance
Many customers operate in regulated industries where governance, transparency, and audit readiness are essential. The 360insights Platform supports compliance with recognized security and privacy standards.
Our governance framework includes documented policies, internal reviews, security training, and evolving controls designed to align with changing regulations and enterprise compliance expectations.

Secure Financial Operations
Many programs managed on the platform involve financial incentives, payments, and rewards, requiring strong safeguards to maintain transaction accuracy and program integrity.
Secure payment workflows, financial approval controls, reconciliation processes, and detailed audit trails help ensure transparency, accountability, and trust for both brands and program participants.

Shared Accountability
Security is a shared responsibility between 360insights and our customers. We secure the platform infrastructure and services that support program operations.
Customers maintain control over program configuration, user access, and data usage, while our teams collaborate closely to ensure security practices align with operational and regulatory requirements.

Trust Supports Growth
Strong security enables confident execution across complex global incentive programs.
By embedding security across the platform architecture, 360insights helps organizations protect data, maintain program integrity, strengthen trust, and scale initiatives without introducing additional operational risk.
Frequently Asked Questions
The 360insights Platform is built with security as a foundational trust layer. Security controls are embedded across our platform, processes, and delivery model to protect sensitive data, financial transactions, and distributed user populations. We maintain independent certifications such as SOC 1, SOC 2, and ISO 27001, and undergo regular third-party audits to ensure ongoing compliance and operational excellence.
360insights supports compliance with leading industry standards, including SOC 1, SOC 2, and ISO 27001. Our platform is designed to help customers meet regulatory requirements across industries and geographies, with documentation and attestation reports available upon request.
The platform applies secure payment processing workflows, financial approval controls, and audit trails to ensure transparency, accuracy, and accountability. These controls support audit readiness and help customers maintain compliance with financial and regulatory standards.
We enforce role-based access controls, secure authentication and authorization, and the principle of least privilege across the platform. Identity and access management is supported by secure integration practices and continuous monitoring to prevent unauthorized access or exposure.
360insights is committed to protecting the privacy of all personal and customer data processed on the 360insights Platform. We apply privacy-by-design and privacy-by-default principles across our products and services, limiting data collection to what is necessary, implementing access controls, and using secure data handling and retention practices.
We support compliance with major data protection regulations such as GDPR and other applicable privacy laws, and we maintain documented policies, processes, and governance frameworks to manage data subject rights, handle data processing activities, and respond to privacy-related inquiries or incidents.
Need More Information? Check Out the Resources Below!
Whether you're looking for industry-specific incentive strategies or want to increase your knowledge, our curated list of resources are designed to answer your most pressing questions.

The Hidden Cost of Disjointed Tech Stacks: Why Unification Matters

5 Things to Consider When Choosing the Right Channel Incentive Management Solution for Your Business
%20copy%204.png?width=768&height=512&length=768&name=Blog_Knowledge%20is%20Power-%20Decreasing%20Risk%20and%20Ensuring%20Data%20Security_Feature%20Image%20(1160x580px)%20copy%204.png)




